- Home
- Tom Clancy
Shadow Warriors: Inside the Special Forces
Shadow Warriors: Inside the Special Forces Read online
Table of Contents
Title Page
Copyright Page
Dedication
I - MONDAY, OCTOBER 7, 1985
II - PIONEERS
III - WARRIORS’ WARRIOR
IV - COUNTRY CARL
V - FEW ARE CALLED, FEWER ARE CHOSEN
VI - VIETNAM
VII - BETWEEN THE WARS
VIII - THE LEBANON TRAGEDY
IX - THE ACHILLE LAURO STRIKE
X - PANAMA: OPERATION BLUE SPOON
XI - PANAMA: OPERATION JUST CAUSE
XII - SHADOWS IN THE STORM
XIII - BULLDOG AND HIS PACK: AN INCIDENT IM THE WAR
XIV - THE FACE OF THE FUTURE
XV - TUESDAY, SEPTEMBER 11, 2001
APPENDIX I: - THE UNITED STATES SPECIAL OPERATIONS COMMAND: A BRIEF HISTORY
APPENDIX II: - LEADERSHIP
Acknowledgements
BIBLIOGRAPHY
INDEX
An unconventional war requires unconventional men—the Special Forces.
Green Berets Navy SEALS • Rangers •
Air Force Special Operations • PsyOps • Civil Affairs •
and other special-mission units
The first two Commanders books, Every Man a Tiger and Into the Storm, provided masterly blends of history, biography, you-are-there narrative, insight into the practice of leadership, and plain old-fashioned storytelling. Shadow Warriors is all of that and more, a book of uncommon timeliness, for, in the words of Lieutenant General Bill Yarborough, “there are itches that only Special Forces can scratch.”
Now, Carl Stiner—the second commander of SOCOM, the U.S. Special Operations Command—and Tom Clancy trace the transformation of the Special Forces from the small core of outsiders of the 1950s, through the cauldron of Vietnam, to the rebirth of the SF in the late 1980s and 1990s, and on into the new century as the bearer of the largest, most mixed, and most complex set of missions in the U.S. military.
These are firsthand accounts of soldiers fighting outside the lines: counterterrorism, raids, hostage rescues, reconnaissance, counterinsurgency, and psychological operations—from Vietnam and Laos to Lebanon, Panama, Saudi Arabia, Kuwait, Iraq, and the new wars of today...
“Some action vignettes from [Special Forces] roots in WWII and Vietnam rival Clancy fiction.”—Kirkus Reviews
“The plethora of insider history and firsthand operation specifics... will please the historically minded.”—Publishers Weekly
NOVELS BY TOM CLANCY
The Hunt for Red October
Red Storm Rising
Patriot Games
The Cardinal of the Kremlin
Clear and Present Danger
The Sum of All Fears
Without Remorse
Debt of Honor
Executive Orders
Rainbow Six
The Bear and the Dragon
Red Rabbit
The Teeth of the Tiger
SSN: Strategies of Submarine Warfare
NONFICTION
Submarine: A Guided Tour Inside a Nuclear Warship
Armored Cav: A Guided Tour of an Armored Cavalry Regiment
Fighter Wing: A Guided Tour of an Air Force Combat Wing
Marine: A Guided Tour of a Marine Expeditionary Unit
Airborne: A Guided Tour of an Airborne Task Force
Carrier: A Guided Tour of an Aircraft Carrier
Special Forces: A Guided Tour of U.S. Army Special Forces
Into the Storm: A Study in Command
(written with General Fred Franks, Jr., Ret., and Tony Koltz)
Every Man a Tiger
(written with General Charles Horner, Ret., and Tony Koltz)
Shadow Warriors: Inside the Special Forces
(written with General Carl Stiner, Ret., and Tony Koltz)
Battle Ready
(written with General Tony Zinni, Ret., and Tony Koltz)
CREATED BY TOM CLANCY
Tom Clancy’s Splinter Cell
Tom Clancy’s Splinter Cell: Operation Barracuda
Tom Clancy’s Splinter Cell: Checkmate
CREATED BY TOM CLANCY AND STEVE PIECZENIK
Tom Clancy’s Op-Center
Tom Clancy’s Op-Center: Mirror Image
Tom Clancy’s Op-Center: Games of State
Tom Clancy’s Op-Center: Acts of War
Tom Clancy’s Op-Center: Balance of Power
Tom Clancy’s Op-Center: State of Siege
Tom Clancy’s Op-Center: Divide and Conquer
Tom Clancy’s Op-Center: Line of Control
Tom Clancy’s Op-Center: Mission of Honor
Tom Clancy’s Op-Center: Sea of Fire
Tom Clancy’s Op-Center: Call to Treason
Tom Clancy’s Op-Center: War of Eagles
Tom Clancy’s Net Force
Tom Clancy’s Net Force: Hidden Agendas
Tom Clancy’s Net Force: Night Moves
Tom Clancy’s Net Force: Breaking Point
Tom Clancy’s Net Force: Point of Impact
Tom Clancy’s Net Force: CyberNation
Tom Clancy’s Net Force: State of War
Tom Clancy’s Net Force: Changing of the Guard
Tom Clancy’s Net Force: Springboard
Tom Clancy’s Net Force: The Archimedes Effect
CREATED BY TOM CLANCY AND MARTIN GREENBERG
Tom Clancy’s Power Plays: Politika
Tom Clancy’s Power Plays: ruthless. com
Tom Clancy’s Power Plays: Shadow Watch
Tom Clancy’s Power Plays: Bio-Strike
Tom Clancy’s Power Plays: Cold War
Tom Clancy’s Power Plays: Cutting Edge
Tom Clancy’s Power Plays: Zero Hour
Tom Clancy’s Power Plays: Wild Card
Most Berkley Books are available at special quantity discounts for bulk purchases for sales promotions, premiums, fund-raising, or educational use. Special books, or book excerpts, can also be created to fit specific needs.
For details, write: Special Markets, The Berkley Publishing Group, 375 Hudson Street, New York, New York 10014.
A Berkley Book
Published by The Berkley Publishing Group
A division of Penguin Putnam Inc.
375 Hudson Street
New York, New York 10014
Copyright © 2002 by C. P. Commanders, Inc.
Passage from Best Laid Plans by David C. Martin and John Walcott,
copyright © 1988 by David C. Martin and John Walcott. .
Chapter II based in part on Hazardous Duty: An American Soldier in
the Twentieth Century, by General John K. Singlaub, U.S. Army (Ret.)
with Malcolm McConnell. Copyright © 1991, used with permission.
All rights reserved.
This book, or parts thereof, may not be reproduced in any form
without permission. The scanning, uploading, and distribution of
this book via the Internet or via any other means without the
permission of the publisher is illegal and punishable by law. Please
purchase only authorized electronic editions, and do not participate in
or encourage electronic piracy of copyrighted materials. Your support
of the author’s rights is appreciated.
BERKLEY and the “B” design are trademarks belonging to Penguin
Putnam Inc.
Clancy, Tom, 1947
Shadow warriors: inside the Special Forces / Tom Clancy, with Carl
Stiner.
p. cm.
Includes bibliographical references.
eISBN : 978-1-436-24570-8
1. Special force
s (Military science)—United States. 2. U.S. Special
Operations Command. 3. Low-intensity conflicts (Military science).
4. United States. Army. Special Forces. I. Stiner, Carl. II. Title.
UA34.S64 C58 2002
356’.16—dc21
2001058914
http://us.penguingroup.com
DEDICATION
This book is dedicated to all the great soldiers, sailors, airmen, and marines with whom and for whom I have been privileged to serve during my thirty-five years of service.
Among these, an elite brotherhood of warriors deserves the highest possible recognition—our nation’s Special Operations Force, past and present.
To those who have sacrificed their lives in the defense of our freedoms, we owe our deepest respect and gratitude. And to their families, we offer our deepest sympathy and prayers for their future.
—General Carl Stiner (Ret.)
AUTHORS’ NOTE
During any given week, an average of more than 3,500 Special Operations Forces (SOF) are deployed overseas in some sixty-nine countries. Their missions range from counterdrug assistance and demining to peacekeeping, disaster relief, military training assistance, and many other special mission activities. As such, they function as instruments of U.S. national policy, and develop relationships with the militaries and governments of the host nations in a way that best serves our national interests now and in the future.
In the writing of this book, we have attempted to include all the information possible about the capabilities of these unique forces, the sacrifices that they make, and the mission areas of their responsibility, as well as just tell some good stories. Needless to say, however, some of these missions and capabilities are sensitive and cannot be revealed for national security reasons. Likewise, the names of some of the personnel, as well as family members, must be protected for personal security reasons. We know the reader will understand that there are some details that are not appropriate for discussion here, and will pardon any necessary omissions.
—Tom Clancy and General Carl Stiner (Ret.)
I
MONDAY, OCTOBER 7, 1985
Brigadier General Carl Stiner, the commander of the Joint Special Operations Task Force, was returning from his morning run at Fort Bragg, North Carolina, when his J-2 intelligence officer, Colonel Mike Flynn, met him at the gate. “A cruise ship has been hijacked in the Mediterranean,” Flynn told him coolly, but with urgency, “and Americans arc very likely on board.”
No other organization had the capability to recapture a ship on the high seas, and Stiner knew they would certainly be called in, and soon.
Stiner was a slender man of six feet, with a crisp but not rigid military bearing and a comfortable, easy look. At the same time, he had always been driven by an underlying intensity and a deep competitiveness. It wasn’t just that he wanted to be the best, or to lead his troops to be the best—all officers want that—but that he had time and again figured out ways to make it happen.
As he and Flynn hurried toward the headquarters building, Stiner was already processing the news. He knew that Flynn’s sparse information was all that was then available, or else Flynn would have told him more. Even so, he had to begin initial actions based on that slender thread. Through long hours of intense planning, training, and rehearsal, JSOTF had developed force packages for virtually any anticipated crisis situation; these were always ready to go within a few hours, as long as there were airplanes available to haul his men. Based on the planning and rehearsals, Stiner focused on what he had to work out right away: “It’s a tough target... got to get more detailed information,” he thought to himself. “We’ll have a long way to go and have to get on the road as soon as possible... must order up airlift now. And we must find out the location of the ship.”
As these thoughts went through his mind, he remained calm. When Special Forces have a job to do, the job must be done fast, accurately, and efficiently. It is likely to be extremely complex, with many lives at risk, and many unknown variables. Facing those conditions, people in these units do not waste their time and effort expressing feelings. They are businesslike, always focusing on the mission at hand—looking especially for vulnerabilities that can be exploited to solve the problem in the cleanest, most complete way possible.
Once he reached the headquarters, he went without pausing to the Joint Operations Center (JOC), a high-tech war room, complete with computer workstations and secure communications to all JSOTF units, the Pentagon, and major commands throughout the world. There he would review the latest intelligence and learn firsthand everything anyone knew about the incident in the Mediterranean. His staff principals had already assembled, waiting for his guidance.
The Task Force maintained its own twenty-four-hour intelligence center, complete with “watch officers”—military officers and civilians expert at picking out intelligence indicators of an impending crisis—analysts, and databases covering every known terrorist organization. Terminals connected the command with all major news networks, including Reuters and the BBC—the first indication of a developing incident often appeared as a news item. JSOTF also had its own people resident in all U.S. intelligence agencies—always looking for indicators of terrorist activities, as well as already existing information that had not seemed important to analysts in those agencies.
In most cases, the headquarters learned of terrorist incidents early, and they usually had the most complete information about them.
Stiner knew that all available intelligence information had already been transmitted by the staff to the units that would be involved. This also meant that all his units would have begun to ready their forces for deployment, while anticipating further guidance from him. They always made maximum use of the time available. In this business, time was a most precious asset.
BEFORE Stiner had taken this command, previous tours in the Middle East had taught him a lot about terrorists and how they operated. For instance, while he had been the chief of training for the modernization of the Saudi Arabian National Guard from 1975 to 1977, he had had a chance to take the measure of Yasir Arafat and his chief lieutenants. Along with other dignitaries from the region, the Palestinians had been invited to a graduation dinner for an officer candidate class by King Khalid and Prince Abdullah, the commander of the National Guard.
Arafat’s lieutenants were impressive, no doubt about it. Most of them had advanced degrees from American universities. They were all well-dressed, very sharp, well-spoken, and knowledgeable about world affairs. Arafat was obviously the leader—and clearly an intelligent and remarkable man—but the lieutenants who made things work struck Stiner as truly formidable. In years to come, that impression proved terribly accurate.
Later, in 1983, Stiner was assigned to Lebanon. There he got a firsthand experience of terrorism and its effects—a U.S. ambassador had been assassinated; while he was there, more than sixty people at the American Embassy. and later more than two hundred U.S. Marines, were killed by bombs.
In those days, Beirut was not only an armed camp with many hostile factions, but a place where fighting might break out anywhere at any time. No one was safe, and death was an ever-present risk—from snipers, crossfires between factions, ambushes, and indiscriminate shelling by heavy artillery and rocket fire. The shelling sometimes involved thousands of rounds, which reduced entire sections of the city to rubble in half an hour.
It was not an casy assignment. Yet, for Stiner, it proved to be rewarding. It offered a chance to learn lessons he could get nowhere else.
You learned how to survive. Or you didn’t.
You learned whom to trust in a life-or-death situation—and whom, by faction or religious motivation, you could not trust.
You learned to think like a terrorist.
THE EVOLUTION OF JSOTF
The traditional function of wars is to change an existing state of affairs. In the early 1970s, a new form of warfare, or maybe a new way of practicing a very old for
m of warfare, emerged—state-supported terrorism. Nations that were not militarily powerful learned to use terrorist tactics to obtain objectives and concessions they could never win through diplomatic or military means.
When this new form of warfare broke out, the United States quickly showed itself unprepared to cope with it. It had neither a national policy nor intelligence capabilities aimed at terrorism, nor any military forces adequately trained and prepared to respond to terrorist provocations. Although the United States was the most powerful nation in the world, its military capabilities were focused on the Soviet Union and not on something like this.
In 1972, Israeli athletes at the Munich Olympics were massacred by Black September terrorists. This outrage might have been avoided if German snipers had had the ability to hit the terrorists as they led the hostages across the airport runway to their getaway plane.
The Israelis took this lesson to heart, and on July 4, 1976, eighty-six Israeli paratroopers landed at Entebbe Airport in Uganda. Their mission was to rescue the passengers from an Air France airliner hijacked eight days earlier. In a matter of minutes, the paratroopers had rescued ninety-five hostages and killed four terrorists—though at the cost of the lives of two hostages and the paratroop commander. News of the raid flashed all over the world—and pointed out even more sharply America’s inadequacies in fighting terrorism.
This truth had already been brought out in May 1975: Forty-one American Marines were killed in an attempt to rescue the thirty-nine crewmen of the American merchant ship Mayaguez after it had been seized by the Cambodian government. The rescue attempt had failed.

 Changing of the Guard
Changing of the Guard Clear and Present Danger
Clear and Present Danger Hounds of Rome
Hounds of Rome Breaking Point
Breaking Point Tom Clancy's Jack Ryan Books 7-12
Tom Clancy's Jack Ryan Books 7-12 Full Force and Effect
Full Force and Effect The Archimedes Effect
The Archimedes Effect Combat Ops
Combat Ops Into the Storm: On the Ground in Iraq
Into the Storm: On the Ground in Iraq Under Fire
Under Fire Point of Impact
Point of Impact Red Rabbit
Red Rabbit Rainbow Six
Rainbow Six The Hunt for Red October
The Hunt for Red October The Teeth of the Tiger
The Teeth of the Tiger Conviction (2009)
Conviction (2009) Battle Ready
Battle Ready Patriot Games
Patriot Games The Sum of All Fears
The Sum of All Fears Fallout (2007)
Fallout (2007) Red Storm Rising
Red Storm Rising The Cardinal of the Kremlin
The Cardinal of the Kremlin Executive Orders
Executive Orders Lincoln, the unknown
Lincoln, the unknown Threat Vector
Threat Vector The Hunted
The Hunted Shadow Warriors: Inside the Special Forces
Shadow Warriors: Inside the Special Forces End Game
End Game Special Forces: A Guided Tour of U.S. Army Special Forces
Special Forces: A Guided Tour of U.S. Army Special Forces Locked On
Locked On Line of Sight
Line of Sight Tom Clancy Enemy Contact - Mike Maden
Tom Clancy Enemy Contact - Mike Maden Fighter Wing: A Guided Tour of an Air Force Combat Wing
Fighter Wing: A Guided Tour of an Air Force Combat Wing Springboard
Springboard Line of Sight - Mike Maden
Line of Sight - Mike Maden EndWar
EndWar Dead or Alive
Dead or Alive Tom Clancy Support and Defend
Tom Clancy Support and Defend Checkmate
Checkmate Command Authority
Command Authority Carrier: A Guided Tour of an Aircraft Carrier
Carrier: A Guided Tour of an Aircraft Carrier Blacklist Aftermath
Blacklist Aftermath Marine: A Guided Tour of a Marine Expeditionary Unit
Marine: A Guided Tour of a Marine Expeditionary Unit Commander-In-Chief
Commander-In-Chief Armored Cav: A Guided Tour of an Armored Cavalry Regiment
Armored Cav: A Guided Tour of an Armored Cavalry Regiment Tom Clancy's Jack Ryan Books 1-6
Tom Clancy's Jack Ryan Books 1-6 The Ultimate Escape
The Ultimate Escape Airborne: A Guided Tour of an Airborne Task Force
Airborne: A Guided Tour of an Airborne Task Force Debt of Honor
Debt of Honor Cyberspy
Cyberspy Point of Contact
Point of Contact Operation Barracuda (2005)
Operation Barracuda (2005) Choke Point
Choke Point Power and Empire
Power and Empire Every Man a Tiger: The Gulf War Air Campaign
Every Man a Tiger: The Gulf War Air Campaign Endgame (1998)
Endgame (1998) EndWar: The Missing
EndWar: The Missing Splinter Cell (2004)
Splinter Cell (2004) The Great Race
The Great Race True Faith and Allegiance
True Faith and Allegiance Deathworld
Deathworld Ghost Recon (2008)
Ghost Recon (2008) Duel Identity
Duel Identity Line of Control o-8
Line of Control o-8 The Hunt for Red October jr-3
The Hunt for Red October jr-3 Hidden Agendas nf-2
Hidden Agendas nf-2 Acts of War oc-4
Acts of War oc-4 Ruthless.Com pp-2
Ruthless.Com pp-2 Night Moves
Night Moves The Hounds of Rome - Mystery of a Fugitive Priest
The Hounds of Rome - Mystery of a Fugitive Priest Into the Storm: On the Ground in Iraq sic-1
Into the Storm: On the Ground in Iraq sic-1 Threat Vector jrj-4
Threat Vector jrj-4 Combat Ops gr-2
Combat Ops gr-2 Virtual Vandals nfe-1
Virtual Vandals nfe-1 Runaways nfe-16
Runaways nfe-16 Marine: A Guided Tour of a Marine Expeditionary Unit tcml-4
Marine: A Guided Tour of a Marine Expeditionary Unit tcml-4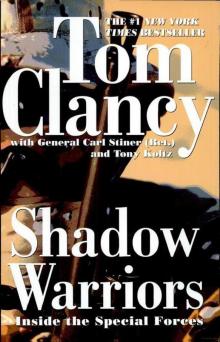 Shadow Warriors: Inside the Special Forces sic-3
Shadow Warriors: Inside the Special Forces sic-3 Jack Ryan Books 1-6
Jack Ryan Books 1-6 Cold Case nfe-15
Cold Case nfe-15 Changing of the Guard nf-8
Changing of the Guard nf-8 Splinter Cell sc-1
Splinter Cell sc-1 Battle Ready sic-4
Battle Ready sic-4 The Bear and the Dragon jrao-11
The Bear and the Dragon jrao-11 Fighter Wing: A Guided Tour of an Air Force Combat Wing tcml-3
Fighter Wing: A Guided Tour of an Air Force Combat Wing tcml-3 Patriot Games jr-1
Patriot Games jr-1 Jack Ryan Books 7-12
Jack Ryan Books 7-12 Mission of Honor o-9
Mission of Honor o-9 Private Lives nfe-9
Private Lives nfe-9 Operation Barracuda sc-2
Operation Barracuda sc-2 Cold War pp-5
Cold War pp-5 Point of Impact nf-5
Point of Impact nf-5 Red Rabbit jr-9
Red Rabbit jr-9 The Deadliest Game nfe-2
The Deadliest Game nfe-2 Springboard nf-9
Springboard nf-9 Safe House nfe-10
Safe House nfe-10 EndWar e-1
EndWar e-1 Duel Identity nfe-12
Duel Identity nfe-12 Deathworld nfe-13
Deathworld nfe-13 Politika pp-1
Politika pp-1 Rainbow Six jr-9
Rainbow Six jr-9 Tom Clancy's Power Plays 1 - 4
Tom Clancy's Power Plays 1 - 4 Endgame sc-6
Endgame sc-6 Executive Orders jr-7
Executive Orders jr-7 Net Force nf-1
Net Force nf-1 Call to Treason o-11
Call to Treason o-11 Locked On jrj-3
Locked On jrj-3 Against All Enemies
Against All Enemies The Sum of All Fears jr-7
The Sum of All Fears jr-7 Sea of Fire o-10
Sea of Fire o-10 Fallout sc-4
Fallout sc-4 Balance of Power o-5
Balance of Power o-5 Shadow Watch pp-3
Shadow Watch pp-3 State of War nf-7
State of War nf-7 Wild Card pp-8
Wild Card pp-8 Games of State o-3
Games of State o-3 Death Match nfe-18
Death Match nfe-18 Against All Enemies mm-1
Against All Enemies mm-1 Every Man a Tiger: The Gulf War Air Campaign sic-2
Every Man a Tiger: The Gulf War Air Campaign sic-2 Cybernation nf-6
Cybernation nf-6 Support and Defend
Support and Defend Night Moves nf-3
Night Moves nf-3 SSN
SSN Cutting Edge pp-6
Cutting Edge pp-6 The Cardinal of the Kremlin jrao-5
The Cardinal of the Kremlin jrao-5 War of Eagles o-12
War of Eagles o-12 Op-Center o-1
Op-Center o-1 Mirror Image o-2
Mirror Image o-2 The Archimedes Effect nf-10
The Archimedes Effect nf-10 Teeth of the Tiger jrj-1
Teeth of the Tiger jrj-1 Bio-Strike pp-4
Bio-Strike pp-4 State of Siege o-6
State of Siege o-6 Debt of Honor jr-6
Debt of Honor jr-6 Zero Hour pp-7
Zero Hour pp-7 Ghost Recon gr-1
Ghost Recon gr-1 Command Authority jr-10
Command Authority jr-10 Tom Clancy's Power Plays 5 - 8
Tom Clancy's Power Plays 5 - 8 Checkmate sc-3
Checkmate sc-3 Breaking Point nf-4
Breaking Point nf-4 Gameprey nfe-11
Gameprey nfe-11 The Hunted e-2
The Hunted e-2 Hidden Agendas
Hidden Agendas Divide and Conquer o-7
Divide and Conquer o-7